
On AliExpress you find cheap wireless (RF433) weather stations compatible with the ‘Fanju’ weather station model FJ3378/74/79C/65/89 (according to AE). Following is the description of the data transmission protocol.
Details
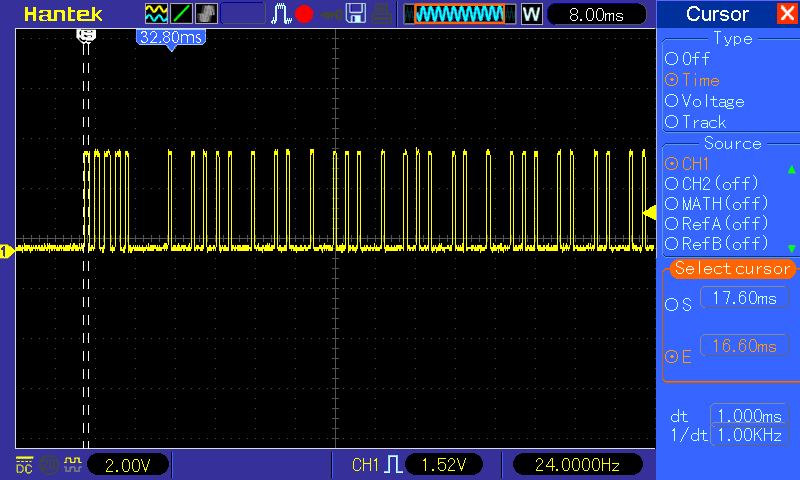
First the RF signal was analysed to determine the physical layer, OOK using e.g. Manchester encoding or pulse-width modulation.
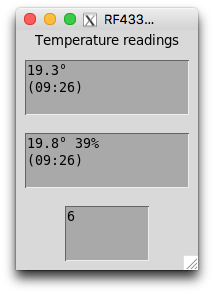
Helpful in reverse engineering a checksum is data differing one bit only. The sensor uses a rolling-code for its identification. That means, when powered off, c.q. batteries are changed, it generates a new id.
With help of the ATTiny and a FET, the sensor is switched off and on for a few hours. The data sent was logged using a Python script. With the thus collected dataset the ‘attack’ started.
To make a long story short, the physical layer uses on-off keying and pulse-width modulation. Pulse durations (mark/space in µs) are as follows (pilight-debug timings between parenthesis):
Sync: 1000/1000 (936/936),
Head: 600/7900 (468/7956)
Data 0: 600/1900 (468/1872)
Data 1: 600/3800 (468/3744-4212)
Tail: 600/16000 (468/15912)
A message comprises 4xSYNC, 1xHEAD, 40xDATA 0/1, 1xTAIL.
Every ±80s the station transmits a burst of six messages.
The checksum turns out to be a Linear-feedback Shift Register (LFSR) hash with seed 0xC and feedback 0x9. The following script calculates the masks used for generating the checksum:
mask = 0xC
print("0")
for i in range(40):
lsb = (mask & 0x1 == 0x1)
mask >>= 1
if lsb:
mask ^= 0x9
print("Mask: {:2x} {:04b}".format(mask, mask))
if ((i + 1) % 4) == 0:
print(i + 1)
Hardware used
Raspberry Pi 4
RF 433MHz superheterodyne receiver *)
ATTiny85 development board *)
A FET and two resistors lying around here
*) AliExpress
Software
A Python script for data analysis and checksum verification
Protocol code has been submitted to the PiLight project and is under review. PiLight GitHub repo
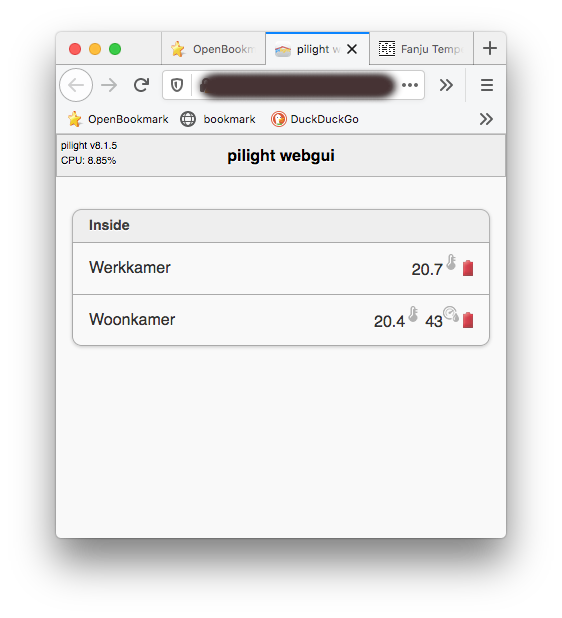
Software
